Stop Governing AI, Start Controlling It
By Matthew Martin
There’s a phrase burned into the brain of every security professional who’s been doing this long enough: compliance does not equal security. In other words, you can’t be secure through documentation. We’ve learned that lesson the hard way, consistently watching organizations pass compliance reviews while still getting breached. A perfectly completed questionnaire has never stopped a ransomware attack. A SOC 2 report has never blocked a credential stuffing campaign. Documentation describes a security posture. It doesn’t create one.
So why are we making the exact same mistake with AI?
Walk into most enterprises today and ask the CISO how they’re managing AI risk. You’ll get variations of the same answer: AI policy drafted, governance committee stood up, use case inventory in progress, waiting on the framework from legal. It’s familiar, it’s comfortable, and it’s insufficient. We are collectively reaching for the governance playbook at the exact moment we need to be reaching for the controls playbook.
The Mental Framework Required
Before we talk about what to do differently, we have to talk about how to think differently.
Governance is a descriptive discipline. It tells you what should happen, who’s accountable, what’s permitted, what gets documented.
Controls are an enforcement discipline. They determine what actually happens, regardless of what the policy says (although hopefully they align).
“Trust but verify” is built into the fabric of every security organization on the planet. In traditional security, we stopped accepting governance as a substitute for controls. We didn’t trust that employees wouldn’t click phishing links, so we built email filtering, MFA, and endpoint detection. We didn’t take a vendor’s word that their software was secure, so we ran vulnerability assessments. We assumed failure and built systems that detected and responded to it. This is the mental framework CISOs need to bring to AI: not “how do we govern this?” but “how do we control it?” Having an AI policy is pointless if that policy is not enforced by anything other than good intentions.
Why Traditional Controls Aren’t Enough and Why Runtime Is the Answer
AI breaks the model we’ve relied on. Traditional security controls were designed for a threat landscape where humans were the primary actors, and even automated attacks operated at a scale our tools were built to handle. AI changes that equation fundamentally.
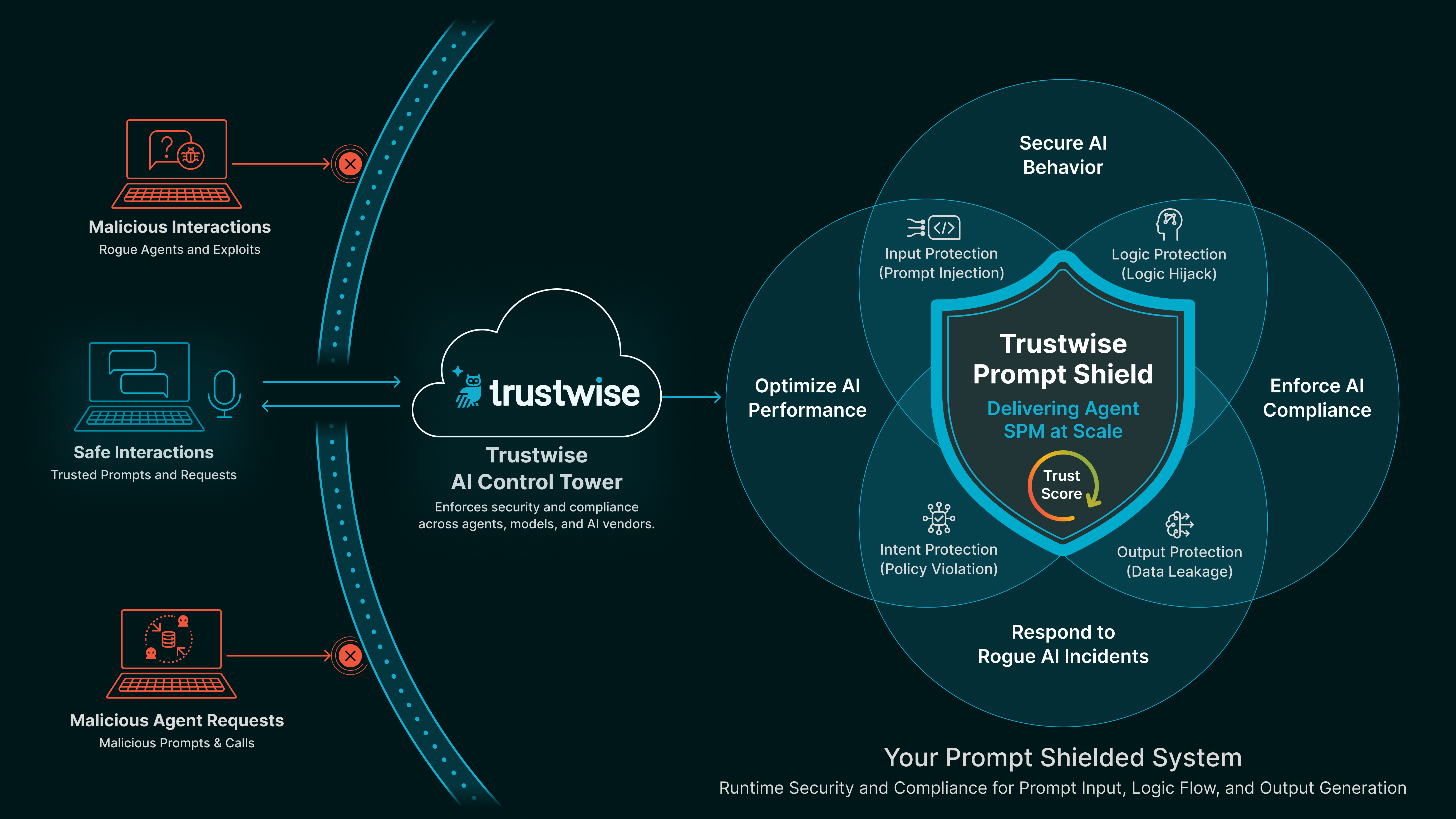
A single AI agent can interact with thousands of data points, make hundreds of decisions, and generate outputs across multiple systems in the time it takes a human analyst to read a dashboard. The risk isn’t just at the point of deployment; it’s continuous, happening in real time, at machine speed. A model that behaves acceptably in testing can behave unexpectedly in production. An agent with appropriate permissions today can be manipulated into misusing them tomorrow.
This is why runtime control is the approach that’s required. It’s not enough to assess an AI system before you deploy it, the same way it’s not enough to scan a network once and declare it secure. You need continuous visibility into what your AI systems are actually doing; what data they’re accessing, what decisions they’re making, what they’re outputting, all while it’s actually happening. Not in the post-incident review. Not in the quarterly audit. Now.
The attack surface for AI isn’t your perimeter. It’s every inference call, every model output, every AI-to-AI interaction in an agentic workflow. Governance frameworks aren’t designed to operate at that speed. Runtime controls are.
Applying the Controls Mindset in Practice
None of this means governance has no role. It sets intent, establishes accountability, and provides the framework within which controls are designed. But it must run in parallel with a controls implementation program, not sequentially.
Start with visibility. You can’t control what you can’t see. Inventory the AI in your environment, not just the enterprise-sanctioned tools, but the shadow AI your employees are already connecting to production systems. Treat AI data flows the same way you’d treat any third-party integration with access to sensitive data. Map what goes in and what comes out.
Then apply the same principles you’d apply to any privileged system: least privilege, behavioral monitoring, anomaly detection, incident response planning. Define what normal looks like for your AI systems and build detection around deviations from it. Test for unexpected behaviors, adversarial inputs, and data leakage with the same discipline you’d bring to penetration testing a critical application.
This is where a platform like Trustwise becomes operationally essential. The gap between having a policy that says models shouldn’t leak sensitive data and having a system that actively monitors for and prevents it in real time is where AI risk lives. Trustwise is built to close it, giving security teams the runtime observability and enforcement layer that translates AI governance intent into actual control. It’s the difference between describing your AI security posture and having one.
AI Control, not Compliance, Frees Innovation
We’ve been here before. We know what happens when an industry responds to a fast-moving threat primarily with documentation. We’ve watched organizations with mature governance programs get breached because the controls weren’t there. We’ve seen compliance become a substitute for security rather than a complement to it.
AI is not going to be different just because we want it to be. Organizations need to treat AI same way they treat every other serious security challenge: with controls that enforce behavior at the speed the technology operates.
The policy binder won’t save you. The governance committee won’t save you. Thinking in terms of controls, not compliance is the way our industry already knows how to operate. We just have to apply it to AI, and in doing so we will set our organizations free to use AI for innovation and new kinds of competitive advantage.
Matthew Martin is the Chief Information Security and Privacy Officer at Western Carolina University.